Since the creation of Bitcoin, the first cryptocurrency, the digital asset ecosystem has grown from zero to over a trillion-dollar industry. However, this rapid growth has attracted attackers and cybercriminals who continually seek new methods to exploit vulnerabilities in users’ Web3 wallets.
As such, it has become imperative for every crypto user to learn the ins and outs of Web3 wallet security. Users must be trained to protect and safeguard their wallets and assets from potential threats.
This article explores the principles of security in Web3 wallets. It offers insight to help users become knowledgeable and cautious as they journey through the intricate Web3 ecosystem.
Understanding the Foundation of Web3 Wallets Security
A Web3 wallet is a digital wallet that holds and stores cryptocurrencies and other digital assets, such as non-fungible tokens (NFTs). At the heart of the Web3 wallet ecosystem lies the bridge between traditional finance and the blockchain universe. In other words, a Web3 wallet is more than just a place to store digital currencies; it is a gateway to a world of decentralized finance (DeFi), digital art ownership, and frictionless cross-border transactions.
Web3 wallets can be broadly categorized into two main types – custodial and non-custodial.
Custodial Wallets
Custodial wallets are similar to digital bank accounts as users trade convenience for control. This means a third party, like a crypto exchange or platform, is responsible for safeguarding your private keys and managing your assets.
While this may seem convenient, allowing users to recover lost passwords quickly and offering instant transaction support, it does relinquish a certain level of control over your assets. Your funds are, in essence, in the hands of another entity, and their security measures will determine the safety of your holdings. Recent history has shown that even the most reputed platforms are not immune to hacks and breaches, putting custodial wallet users at some risk. Examples of popular custodial wallets include exchanges like Binance and Coinbase, and one example of an institutional custodian wallet is Fireblocks.
Non-Custodial Wallets
Non-custodial wallets, also known as self-custodial, place control firmly in the hands of the wallet holder. You are the sole custodian of the private keys necessary to access and manage your crypto assets. This setup offers higher security as your funds are not susceptible to breaches targeting third-party services. However, it comes with the responsibility of safeguarding your wallet, refraining from getting scammed, and storing your keys diligently. Losing access to your private keys means losing access to your funds forever. Non-custodial wallets can take various forms, such as mobile or desktop application wallets and hardware wallets (physical devices that store your keys offline).
Hot Vs. Cold Wallets
Web3 wallets can also be grouped into hot wallets and cold wallets.
Hot wallet
A hot wallet is a crypto wallet whose private key was created from a device connected to the internet. The hot wallet is used for active trading activities and interacting with decentralized applications (dApps) in smaller amounts. The benefits of using a hot wallet include easy accessibility and a structured user interface. The major downside, however, is that hot wallets are easier to exploit.
Cold wallet
A cold wallet is a type of crypto wallet whose private key creation is done offline and is primarily used for long-term storage of digital assets and for trading higher amounts.
Cold wallets store private keys offline, making them less susceptible to hacking and online threats. They can be in the form of hardware devices or paper wallets. Despite the high-security strength, cold wallets are not suitable for quick and frequent transactions.
Web3 Wallet Security Threats
The safety of users’ digital assets relies heavily on the robustness of Web3 wallet security measures. While some wallets provide more security, many Web3 wallets are not hack-proof. As such, it has become crucial for investors to take necessary actions to safeguard their wallets. This includes understanding the different malicious schemes being used by bad players, identifying vulnerabilities that can come from the user’s end, and implementing solutions to mitigate the risks.
Exploits by Hackers
Hackers are constantly looking for weaknesses in Web3 wallets and dapps. These nefarious players use different tricks to do this, so it’s crucial to be careful and informed. For example, hackers are likely to seek for flaws in smart contract codes to exploit Web3 platforms for malicious purposes. Some of these vulnerabilities include re-entrancy or integer-overflow bugs.
Another example is the supply chain attack. This happens when hackers target the entire process of making and sharing wallet apps. They can introduce backdoor malicious code or vulnerabilities during the wallet development and ensure the compromised wallets are distributed to users.
User-side Vulnerabilities
Phishing Attacks: Phishing is a significant problem in the Web3 ecosystem. Hackers create fake websites that look like the original website and messages that look real to lure investors into revealing their private keys or make them interact with the dapp, not knowing that signing such transactions will drain their wallets.
Malicious Browser Extensions: Malicious browser extensions are a favorite tool for Web3 hackers. Just as the phishing sites, these extensions are presented as legitimate wallet extensions or dapp integrations. However, they aim to exploit your PC and have you sign malicious transactions to drain your wallet. This is why users must be cautious when adding browser extensions to their devices.
Social Engineering Attacks: Hackers sometimes trick people into sharing confidential information. These bad actors might pretend to be someone trustworthy to get your wallet details or control your computer. This is why it is crucial to be skeptical of unsolicited requests for information.
Lack of Understanding: DeFi platforms have gained significant popularity in the Web3 ecosystem, allowing users to earn returns on their crypto assets through various liquidity provision mechanisms, yield farming, and decentralized exchanges. However, these new yield options also come with risks and complexities, and a lack of knowledge can result in costly errors.
For example, putting your crypto assets into a low-liquidity pool on platforms like Uniswap can be risky. Low-liquidity pools can make it harder to withdraw assets without causing price swings and potential losses due to “impermanent loss.” To avoid these errors, it’s crucial to understand how DeFi works, assess risks, start with small amounts, and seek advice from experienced users.
Related: Understanding User-Level Crypto Attack Terms
Solutions for Web3 Wallet Security Threats
Thankfully, there are safety measures that can be taken to safeguard oneself from these attacks and vulnerabilities. They include:
Master the Wallet’s User Interface
The success of a user’s on-chain experience lies heavily on their familiarity with the features within their wallet. Most wallets offer a quick tour or deep documentation tour to help users get conversant with the functions of storing and interacting with their digital assets.
A missclick on a malicious transaction – can end the crypto journey of new users.
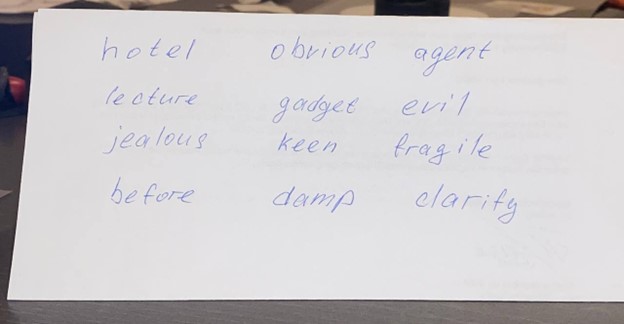
Never Share Private Keys. With Anyone
The idea of not sharing private keys cannot be over-emphasized. The private keys are a set of alphanumeric codes generated using cryptographic algorithms, which are represented by a secret recovery phase of 12/24 words. They are unique to an individual user and hold access to all the assets stored in the wallet.
Scammers may pose as customer care representatives for a Web3 wallet and request for a user’s private keys to fix an issue. If such a thing should happen, every user is advised never to share their private keys. And never store or make a backup on your PC or mobile device.
Do Not Connect to Unverified or New dApps
To conduct some sophisticated phishing attacks, attackers often create malicious dApps whose interfaces are the spitting image of a real dApp. Like the original dApp, the suspicious application will request that users connect their Web3 wallets to the platform. Connecting to such protocols puts a user in a vulnerable position. Verifying the dApp URL before connecting is key to protecting oneself from such attacks.
Never Open Any File You’re Not Sure About
Any innocent PDF can ruin your PC. Of course, executable files, like in this case, can cause harm to your wallets and drain them. It’s important to make sure you trust the sender and don’t take chances. If it’s not necessary – do not run files.
Use Web3 Security Solutions
Despite the best efforts of users, there is always the tendency to miss a malicious trace and eventually fall prey to attackers. That is where Web3 wallet security solutions come in. They are Web3 tools and services put in place to easily identify and mitigate risks from bad players. A primary example is Blockfence, a web extension installed on a device to conduct risk assessments and bolster end-to-end user protection. You can also install Blockfence as a plugin to your Metamask as a snap.
The Current Security Status of Top Web3 Wallets
MetaMask: The most popular self-custodial wallet allows users to access their accounts via secret recovery phrases. There is also a provision for users to fortify their wallet security with passwords and biometric scans. MetaMask provides frequent updates to make users’ experience while using the platform as intuitive as possible.
Unlike hardware wallets, MetaMask does not have a two-factor authentication (2FA) security feature for additional protection.
Metamask recently added support to Metamask Snaps, which are plug-ins on top of Metamask. Among those, there are security-related Snaps.
Coinbase Wallet: This self-custodial wallet, by the popular exchange, gives users full responsibility for safeguarding their digital assets. For this reason, the platform does not support 2FA. Nonetheless, the wallet provides other security measures, such as biometric scans, security locks, and passwords – on the wallet level.
On the transaction level, Coinbase Wallet alerts users when they connect their wallet addresses to a suspicious dApp. The wallet also hides malicious airdrops from users’ list of assets.
Coinbase Wallet also has a history of providing users with a great UX.
Trust Wallet: This is another popular wallet among Web3 users. The self-custody platform supports several user’s side security measures, including biometrics, passcodes, and prompts when connecting with new dApps. The wallet uses the security scanner to detect potential risks in transactions and alert users.
Trust Wallet supports 2FA when users want to confirm transactions. The platform also allows for a seamless user experience through its intuitive interface. The wallet also has a feature that enables users to revoke their smart contracts allowance, reducing their exposure to smart contract exploits.
Phantom Wallet: Phantom operates as a non-custodial wallet that supports the Solana blockchain and EVM-based blockchains.
The wallet enables security features like passwords and biometrics scans. Phantom also safeguards users from security risks by alerting them about potential risks when connecting to malicious applications. This protects users from potential phishing exploits. Users’ reviews also show that Phantom’s UX is intuitive.
Account Abstraction: The Future of Web3 Wallets?
Presently, most Web3 wallets strive to bolster their security layers, frequent security patch updates, and timely reminders to their users about the need for Web3 wallet security. More Web3 wallets will likely introduce more security measures in future upgrades.
Web3 wallets may also support account abstraction for future updates. Account abstraction enables the creation of smart accounts by separating the tasks of initiating a transaction from covering the transaction fees between two accounts. These accounts can either be externally owned accounts (EOA) or smart contracts. By leveraging account abstraction, Web3 wallet creators can offer their users an added security layer, ensuring that only secured transactions can pass through. AA also enables a better UX for self-custody, allowing for social recovery in case the user loses his private keys.
Conclusion
As the Web3 space continues to evolve, there will be a need for adequate Web3 wallet security measures to ensure users’ on-chain safety. This article identified several threats that could come from hackers and wallet holders. It also discussed solutions to these threats.
As you choose a Web3 wallet to entrust your assets, be sure to conduct due diligence and use a platform that will favor you in the long run.